In case you are nonetheless appending the present 12 months to the top of your password, you aren’t slick, and also you definitely aren’t safe. Based on new analysis from cybersecurity agency Kaspersky, we’re caught in a harmful loop of dangerous digital hygiene, recycling credentials that hackers have recognized about for years.
The info, which analysed main password leaks from 2023 by 2025, paints a grim image of human behavior. The headline determine is alarming: 54 per cent of the compromised passwords present in 2025 leaks had already been uncovered in prior information breaches.
This means that for almost all of customers, the issue isn’t simply that they’re being hacked; it’s that they’re utilizing keys that had been stolen years in the past. Kaspersky claims the common lifespan of a password present in these dumps is between 3.5 and 4 years. In web time, that’s an eternity.
The ‘12345’ Downside
Regardless of years of warnings, multi-factor authentication (MFA) pushes, and the rise of biometrics, the password stays the first methodology of authentication for many – and we’re horrible at creating them.

Kaspersky’s evaluation discovered that customers are nonetheless counting on predictable patterns that make brute-force assaults (the place hackers use software program to guess thousands and thousands of mixtures a second) trivially simple. The commonest offender stays the sequence ‘12345’.
However it will get extra particular. We tend to anchor passwords to time.
10 per cent of the passwords analysed contained a quantity resembling a date between 1990 and 2025.0.5 per cent of all leaked passwords ended particularly with “2024”. Which may sound small, but it surely means each 2 hundredth password is basically the identical guessable string.
Frequent nouns like “love”, names of nations, and private names additionally characteristic closely. Whenever you mix a typical phrase with a predictable date suffix, you aren’t making a stronghold; you might be making a welcome mat.
The Pivot to Passkeys
This inertia is precisely why the business – together with Google, Apple, and Microsoft – has been aggressively pushing towards passkeys, a normal that replaces the typed password fully.
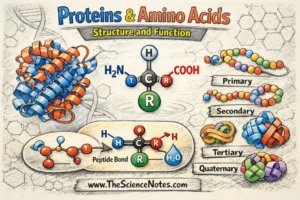
In contrast to a password, which is a shared secret ( it, the server is aware of it), a passkey makes use of public-key cryptography. Whenever you set one up, your system generates a singular pair of cryptographic keys. The personal key stays in your system and by no means leaves. The public key is shipped to the service you might be logging into.
Whenever you attempt to log in, the service sends a mathematical problem. Your system solves it utilizing the personal key, normally unlocked by way of an area biometric verify like a fingerprint or Face ID. As a result of the server by no means holds your personal key, there may be nothing for hackers to steal in a server breach. It’s also phishing-resistant; a passkey for google.com merely gained’t work on a pretend website like g00gle.com.
Kaspersky’s Implementation
This brings us to the software program replace accompanying the analysis. Kaspersky is updating its Password Supervisor to completely assist passkeys throughout all platforms.
Whereas passkeys are safe, the early consumer expertise has been fragmented. A passkey created on an iPhone is saved in iCloud Keychain, which makes it annoying should you then wish to log in on a Home windows PC or an Android pill. Third-party managers like 1Password, Bitwarden, and now Kaspersky, are attempting to bridge that hole by syncing passkeys throughout totally different ecosystems.
The brand new replace permits customers to create, retailer, and sync passkeys immediately throughout the Kaspersky app. This implies should you generate a passkey in your telephone, it’s synchronised and out there to unlock your account in your desktop, bypassing the platform restrictions of Apple or Google.
Marina Titova, VP for Client Enterprise at Kaspersky, frames the replace as a obligatory evolution to cease the “juggling” of logins that results in the fatigue – and the dangerous habits – highlighted of their report.
The characteristic works equally to current password flows: you replace the app, grant permissions, after which comply with the prompts on supported web sites to interchange your static password with a cryptographic key.
Associated